Data Flow Diagram Cyber Security Security Conceptdraw Firewa
Cyber security flow chart Security cyber network tips cybersecurity computer steps infographic diagram degrees diagrams conceptdraw example networks solutions architecture solution information risks threats Architecture cybersecurity enterprise iot cyber security diagram system software
Network Security Tips
Data flow diagram in software engineering Cybersecurity and digital business risk management flow diagram of Process flow vs. data flow diagrams for threat modeling (2023)
Cybersecurity incident response plan template and example uk
Network security modelCyber security: a paradigm shift in it auditing Risk assessment flowchart for cyber security managementSecurity event logging, why it is so important – aykira internet solutions.
Flow chart of cyber investigation : cyber crime awareness societyCyber security flowchart Network security modelCyber security diagram.

Network security
Cyber security threats and data flow diagramsIncident cyber response template plan structure immediately planning usable guidance Cybersecurity policies & proceduresCyber security flow chart.
Flow chart on cyber security from research paperNetwork security tips Cyber incident flow chartData flow diagram.

Cyber security flow chart
Rfid vm security system flow chartCrime evidence ipc Flow cybersecurity chartSecurity flow cyber data event logging diagram logs internet important why so together putting events au.
Rfid vmCyber security incident response process flow chart deploying computer Flow chart cyber security compromise australiaSecurity network diagram model cloud diagrams government computer solution devices conceptdraw example access networks architecture solutions cybersecurity information models examples.
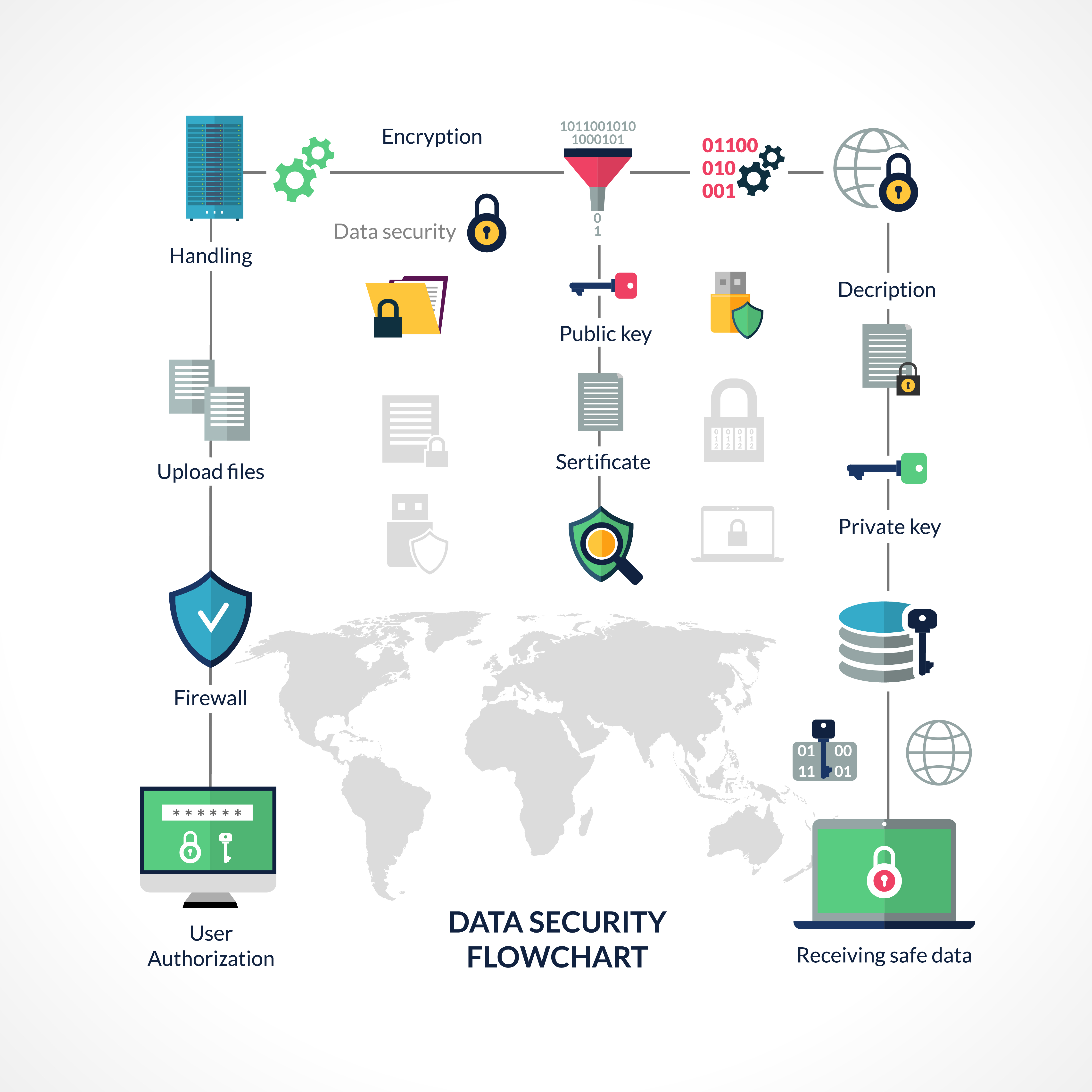
Cyber security flowchart royalty free vector image
Iot & enterprise cybersecurityFree vector Cyber security isometric flowchart royalty free vector imageSecurity conceptdraw firewall firewalls architectures infrastructure networking systems lan devices create wan protecting realtek privacy.
Data flow diagram of smart security frameworkSecurity network diagram control computer diagrams devices networks secure access encryption solution cloud examples model architecture example conceptdraw software system Cyber security framework mind map templateNist cybersecurity framework.

Cyber security compromise flow chart
Data flow and security overviewCyber security incident response process flowchart ppt powerpoint Cybersecurity procedures implementation yokogawa customer developing implement solutions benefits accordance practices.
.


Free Vector | Isometric cyber security flowchart composition of

Process Flow vs. Data Flow Diagrams for Threat Modeling (2023)

Cybersecurity Policies & Procedures | Yokogawa Electric Corporation

cybersecurity-flow-chart | Cheryl D. Calhoun

Cybersecurity And Digital Business Risk Management Flow Diagram Of

Cyber Incident Flow Chart

Cyber Security Compromise flow chart - Cyber Insurance Australia